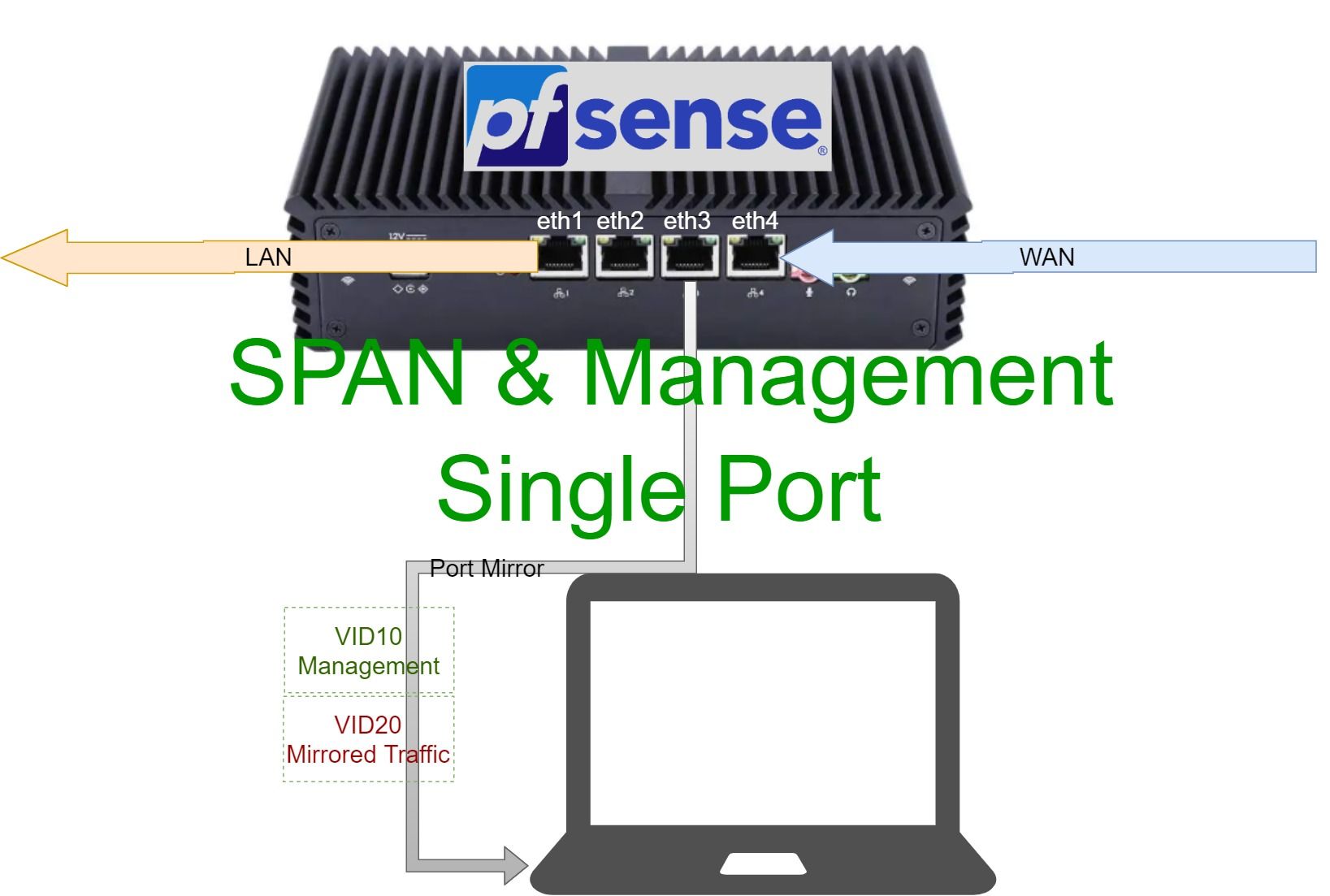
Port Mirror (SPAN) and management on a single physical port
Want to setup a SPAN port for your network analyzer but you are hardware limited to a single physical port? This will walk you through setting up a software SPAN port on PfSense.
TL;DR
Use software port mirroring if you don't have an advanced network switch, one example is ifconfig utility in UNIX like systems. PfSense FTW.
Introduction
I was trying to setup and evaluate Security Onion v2, I had a spare laptop lying around to test with, but it only has one physical port and a WiFi adapter. Security Onion requires at least 2 Ethernet NICs, one for management and the other for traffic monitoring (RX mode only).
I tried playing with the Wifi adapter under a Windows VM running alongside SO under an ESXi host, but that looked ugly and too complicated. Instead, I considered the following approach:
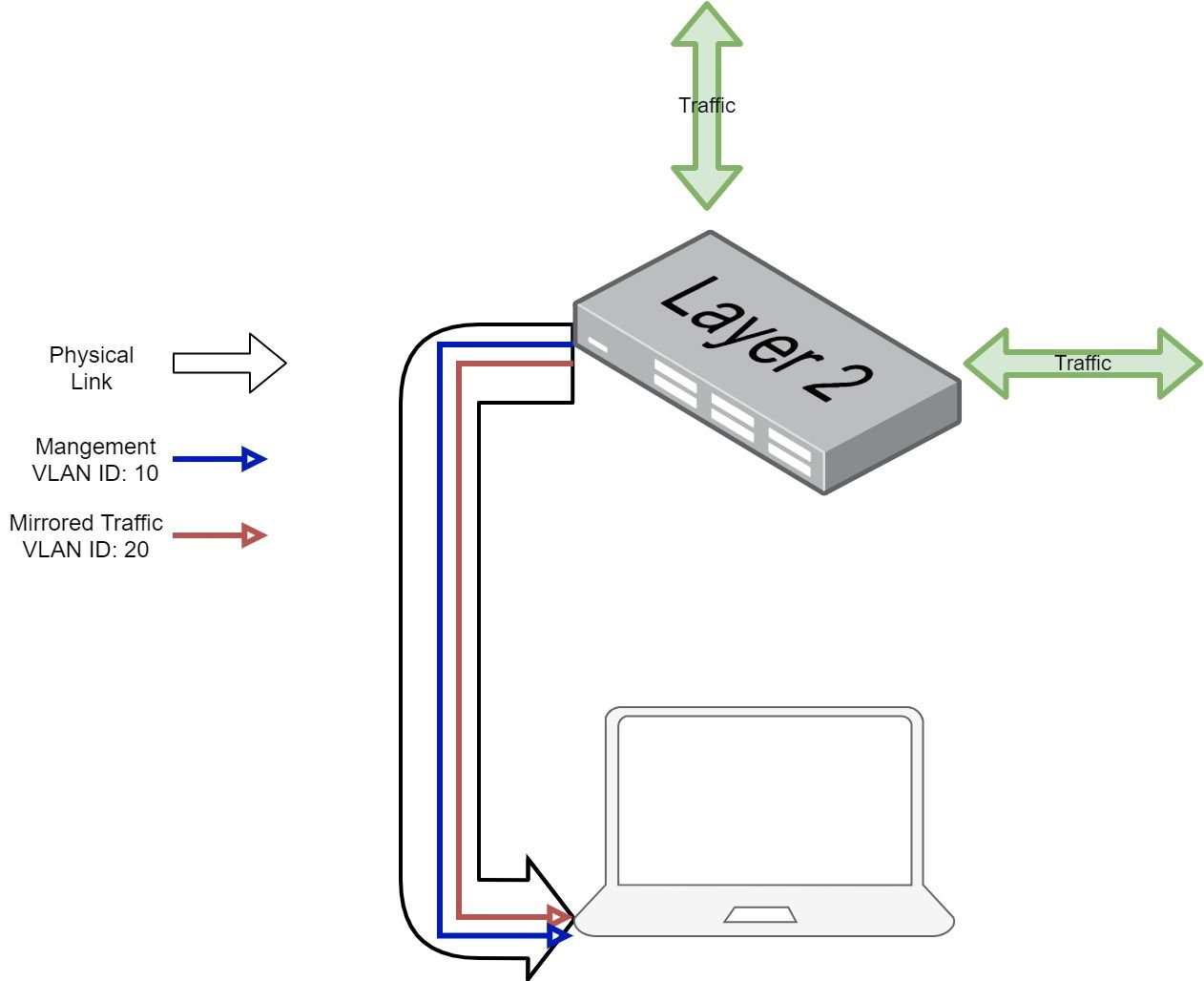
To Achieve this, we need a layer 2 switch that supports port mirroring and can send mirrored traffic to a specific VLAN while still forwards and receives frames on the parent physical port. I believe this is only supported on very advanced enterprise gear like some high end Cisco switches (some flavor of RSPAN). Even then, additional features need to be supported by the switch like QinQ in order to mirror sub-interfaces.
I only had a Unifi switch that barely supports standard physical port mirroring, so the hardware option is not available.
What about a software port mirror?
It is possible to do port mirroring in software. In FreeBSD, ifconfig package provides an option to mirror a bridge port to another interface. I am going to walk through how to do it in Pfsense, since it uses ifconfig in the backend and it will be easier to setup and configure.
Prerequisite:
- a PfSense box with at least one unused Ethernet port.
First, let's get things clear by looking at our setup:
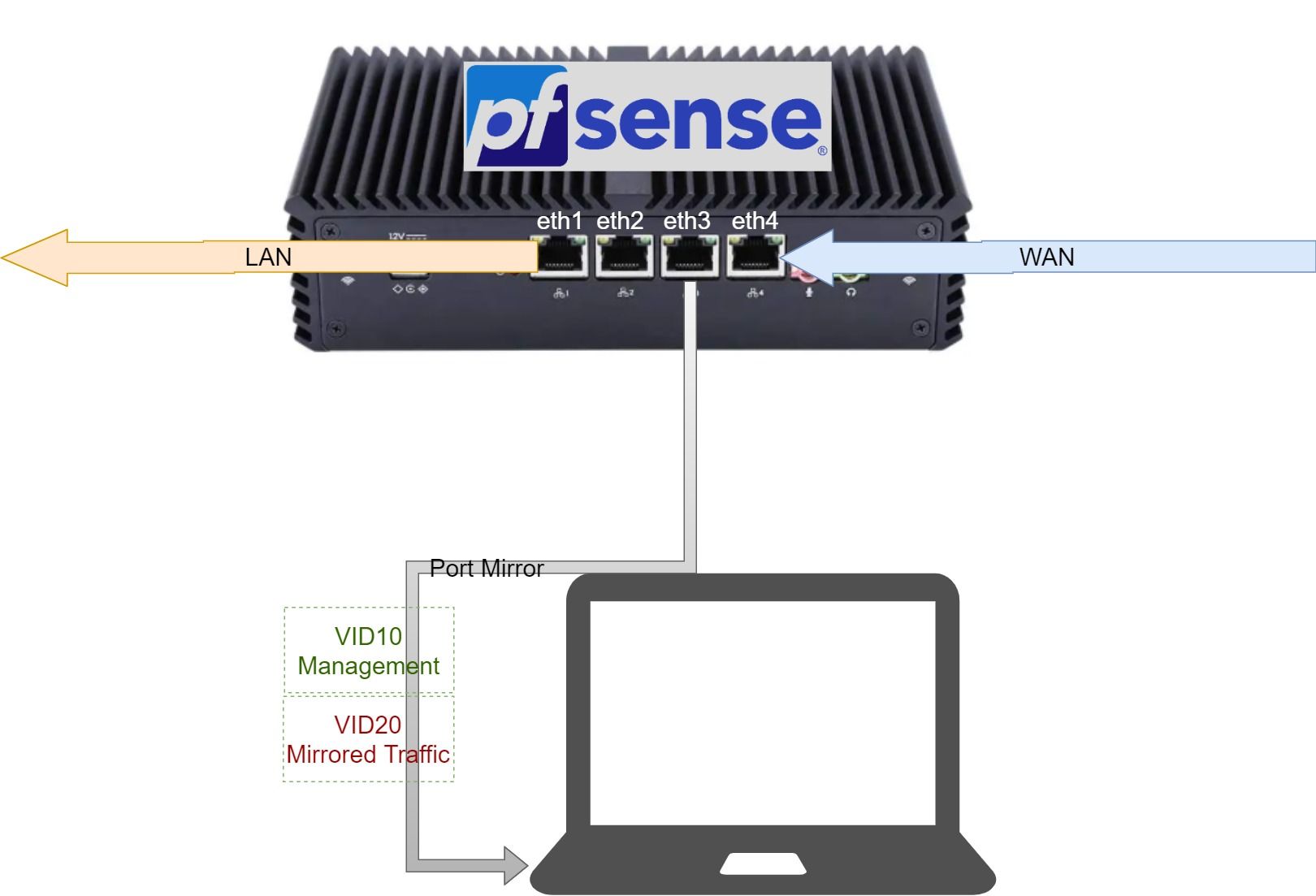
We need to connect our pfsense box directly to the analyzer device, not through a layer 2 switch.
First, we need to define our VLANs under the physical port eth3, in our case we need two:
Interface>Assignments>VLANs>Add
Then we assign an ip address to the management vlan and enable it . For the SPAN vlan, we only need to enable it, without assigning addresses.
To send mirrored traffic to the SPAN vlan, we first need to create a bridge interface, then add the LAN interface (or the one to be mirrored) to that bridge. The process is as follows:
Interface>Assignments>Bridge>Add, and choose the LAN interface as a member, then toggle 'Display Advanced', and under Span port option, choose the SPAN VLAN that we created earlier.
Last step is to assign and enable the bridge interface that we created, without assigning addresses to it.
If more than one interface needs to be mirrored, each mirrored interface has to be on a different bridge, while all can share the same SPAN VLAN.
Now anything enters or leaves the bridge interface is mirrored to the SPAN VLAN. The pfsense part is done, for the analyzer device end, we need to configure its interfaces.
For my specific setup, I use Security Onion as a VM under ESXi, so all I had to do was configure ESXi management interface and give SO VM two network connections, one management with VID 10, and the other SPAN with VID 20.
Caveat when using this approach
Sub-interfaces of the original interface to be mirrored do not get replicated to the SPAN VLAN. For example, in our setup, if the LAN interface had VLAN interfaces under it, they would not be mirrored to the SPAN VLAN.
To circumvent that, we could use QinQ (802.11ad) which is essentially a second VLAN layer. However, this will require some changes to the existing setup and interface reassignments (reassigning LAN to be under a QinQ interface). In most cases this will only be done in a lab, so if you want to mirror more than one interface, it might be easier to just add multiple bridge interfaces than deal with QinQ complexities.
